-
Notifications
You must be signed in to change notification settings - Fork 37
(MODULES-10986) Fix gMSA username support #188
New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Conversation
Since the enhancement intended to help sysadmins, pulled in as puppetlabs#150: When not setting a password, this is interpreted as "Run only when user is logged on". When configuring a scheduled task to use a Group Managed Service Account (gMSA) principal, there is no password to provide. The scheduler will get the password automatically when properly configured, and should be able to run the task even though the service account is not "logged on". Otherwise, the Managed Service Account is never "logged on" so the task does not run on expected schedule. It does not seem viable to add a proper test case for this particular situation without an AD domain configuration and a proper gMSA in place. Without a correct gMSA, an error message stating "No mapping between account names and security IDs was done" appears to be returned.
scheduled_task is a typeBreaking changes to this file MAY impact these 10 modules (near match):This module is declared in 0 of 576 indexed public
|
|
Hi @sigv, thank you for submitting this PR, I'm trying now to test it |
|
For testing this, you would be expected to have a domain, as mentioned. # Something like this will get the job done:
Add-KdsRootKey –EffectiveTime ((Get-Date).AddHours(-10))Then for setting up the Service Accounts you can use New-ADServiceAccount -Name svc_account -Enable $True -DNSHostName svc_account.example.com
Set-ADServiceAccount -Identity svc_account -PrincipalsAllowedToRetrieveManagedPassword 'Some Server Group'
For the resource itself, you can then use something along the lines of: scheduled_task { 'Test scheduler':
command => 'C:\\Windows\\System32\\test.exe',
working_dir => 'C:\\Windows\\System32',
user => 'EXAMPLE\\svc_account$',
compatibility => 3,
enabled => 'true',
trigger => [{
schedule => 'daily',
start_time => '05:00'
}],
} |
|
Hi @sigv, thank you for providing me all the information, I was able to set up my environment and the AD domain, let me try and add Add-KdsRootKey and set up the Service Accounts, thank you for all your help! |
|
@daianamezdrea, any luck? 🤞🏻 |
|
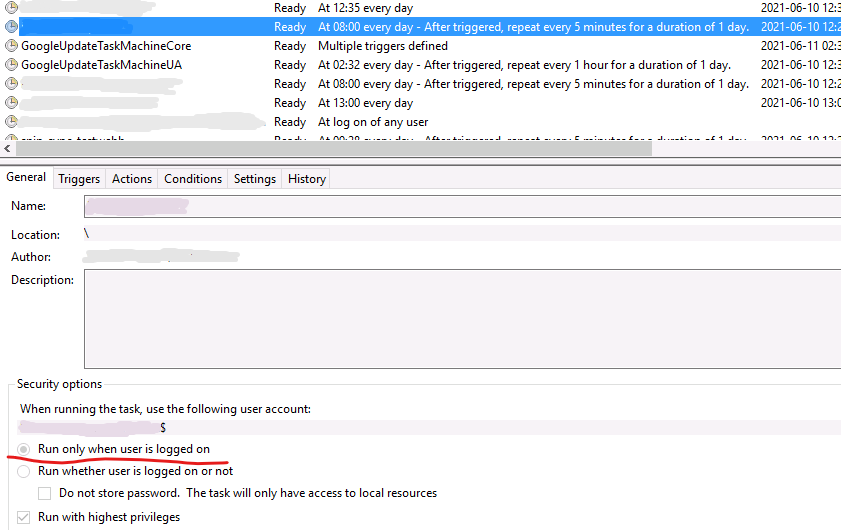
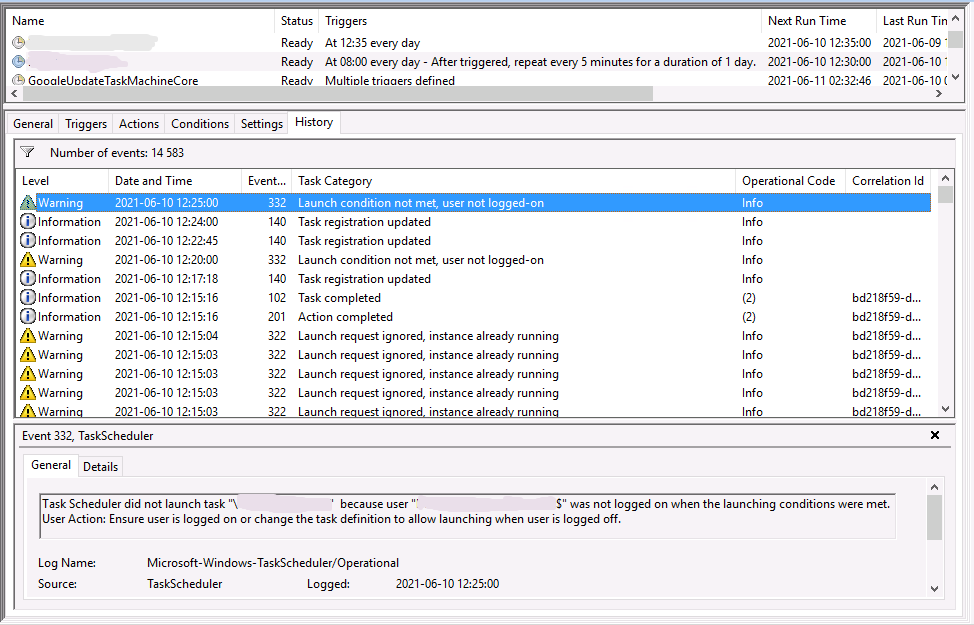
I can confirm that this pull request solved the problem for me on version 3.0.0 of the module. First of all the modules documentation wasn't clear that you needed to not use the Before applying this pull request the module sets the scheduled task to "Run only when user is logged on": And this doesn't work on a gMSA's as shown in the History of the scheduled task: But by applying @sigv fix it solved my problem by setting the task correctly to "Run whether user is logged on or not". So I would like to see this pull request implemented in a new release of the module as well. |
|
@sigv @JohnEricson thank you both for your time and work. The fix will be released on the next community day (Monday). |
Since the enhancement intended to help sysadmins, pulled in as #150: When not setting a password, this is interpreted as "Run only when user is logged on".
When configuring a scheduled task to use a Group Managed Service Account (gMSA) principal, there is no password to provide. The scheduler will get the password automatically when properly configured, and should be able to run the task even though the service account is not "logged on". Otherwise, the Managed Service Account is never "logged on" so the task does not run on expected schedule.
It does not seem viable to add a proper test case for this particular situation without an AD domain configuration and a proper gMSA in place. Without a correct gMSA, an error message stating "No mapping between account names and security IDs was done" appears to be returned.