You signed in with another tab or window. Reload to refresh your session.You signed out in another tab or window. Reload to refresh your session.You switched accounts on another tab or window. Reload to refresh your session.Dismiss alert
@@ -2367,35 +2367,71 @@ By tracking intent states, XMTP ensures that if an app crashes before a commit h
2367
2367
## pages/protocol/overview.mdx
2368
2368
# XMTP protocol overview
2369
2369
2370
-
XMTP is a decentralized messaging protocol that enables secure, end-to-end encrypted communication between blockchain addresses. This section covers the technical foundations and implementation details of how XMTP works under the hood.
2370
+
XMTP is a decentralized messaging protocol that enables secure, end-to-end encrypted communication between any identities that can produce a verifiable cryptographic signature.
2371
2371
2372
-
## Architecture fundamentals
2372
+
XMTP implements [Messaging Layer Security](https://messaginglayersecurity.rocks/) (MLS), which is designed to operate within the context of a messaging service. As the messaging service, XMTP needs to provide two services to facilitate messaging using MLS:
2373
2373
2374
-
With XMTP, messages are routed through **[topics](/protocol/topics)**, which are unique addresses that identify conversation channels. Messages are packaged as **[envelope types](/protocol/envelope-types)** that contain the actual message data plus metadata for routing and processing.
2374
+
- An [authentication service](https://messaginglayersecurity.rocks/mls-architecture/draft-ietf-mls-architecture.html#name-authentication-service)
2375
+
- A [delivery service](https://messaginglayersecurity.rocks/mls-architecture/draft-ietf-mls-architecture.html#name-delivery-service)
2375
2376
2376
-
The protocol prioritizes **security** through advanced cryptographic techniques, delivering end-to-end encryption for both 1:1 and group conversations. To learn more, see XMTP's [security properties](/protocol/security) and how [wallet signatures](/protocol/signatures) authenticate users.
2377
+
This section covers the elements of XMTP that provide these services.
2377
2378
2378
-
## Group messaging mechanics
2379
+
:::info[Who should read these docs]
2379
2380
2380
-
For group conversations, XMTP introduces sophisticated state management:
2381
+
This protocol documentation is designed for:
2381
2382
2382
-
- **[Epochs](/protocol/epochs)** represent the cryptographic state of a group at any point in time. Each group operation (like adding members) creates a new epoch with fresh encryption keys. This concept comes from [Messaging Layer Security](https://messaginglayersecurity.rocks/), which XMTP builds upon.
2383
+
- Protocol contributors working on XMTP's core implementation
- Anyone curious about the technical details behind XMTP's messaging
2383
2386
2384
-
- **[Intents](/protocol/intents)** provide reliable state management through an internal bookkeeping system that handles retries, crashes, and race conditions when applying group changes.
2387
+
For most developers, the [Build chat apps](/chat-apps/intro/get-started) and [Build agents](/agents/get-started/build-an-agent) sections provide the practical guidance needed to build with XMTP.
2388
+
2389
+
:::
2390
+
2391
+
## Encryption
2392
+
2393
+
The encryption elements are mainly defined by MLS, with some additions by XMTP. To learn more, see:
2394
+
2395
+
- [Security](/protocol/security)
2396
+
2397
+
XMTP and MLS prioritize security, privacy, and message integrity through advanced cryptographic techniques, delivering end-to-end
2398
+
encryption for both 1:1 and group conversations
2399
+
2400
+
- [Epochs](/protocol/epochs)
2401
+
2402
+
Represent the cryptographic state of a group at any point in time. Each group operation (like adding members) creates a new epoch with fresh encryption keys
2403
+
2404
+
- [Envelope types](/protocol/envelope-types)
2405
+
2406
+
Messages are packaged as envelope types that contain the actual message data plus metadata for routing and processing.
2407
+
2408
+
## Identity
2409
+
2410
+
The identity elements are mainly defined by XMTP. To learn more, see:
2411
+
2412
+
- [Inboxes, identities, and installations](/protocol/identity)
2413
+
2414
+
The identity model includes an inbox ID and its associated identities and installations.
2415
+
2416
+
- [Wallet signatures](/protocol/signatures)
2417
+
2418
+
Authenticate users using verifiable cryptographic signatures.
2419
+
2420
+
## Delivery
2385
2421
2386
-
- **[Cursors](/protocol/cursors)** enable efficient message synchronization by tracking where each client left off when fetching new messages.
2422
+
The delivery elements are mainly defined by XMTP. To learn more, see:
Messages are routed through topics, which are unique addresses that identify conversation channels.
2427
+
2428
+
- [Cursors](/protocol/cursors)
2429
+
2430
+
Enable efficient message synchronization by tracking where each client left off when fetching new messages.
2431
+
2432
+
- [Intents](/protocol/intents)
2433
+
2434
+
Provide reliable groupstate management through an internal bookkeeping system that handles retries, crashes, and race conditions when applying group changes.
- **Anyone curious** about the technical details behind XMTP's messaging
2420
-
2421
-
For most developers, the [Build chat apps](/chat-apps/intro/get-started) and [Build agents](/agents/get-started/build-an-agent) sections provide the practical guidance needed to build with XMTP.
2422
-
2423
2449
2424
2450
## pages/protocol/xips.mdx
2425
2451
# XMTP Improvement Proposals (XIPs)
@@ -2593,6 +2619,99 @@ Here is a summary of individual cryptographic tools used to collectively ensure
2593
2619
2594
2620
Used for quantum-resistant key encapsulation in Welcome messages. XWING is a hybrid post-quantum KEM that combines conventional cryptography with [ML-KEM](https://csrc.nist.gov/pubs/fips/203/final) (the NIST-standardized post-quantum component), providing protection against future quantum computer attacks while maintaining current security standards.
2595
2621
2622
+
## FAQ about messaging security
2623
+
2624
+
1. **Can XMTP read user messages?**
2625
+
2626
+
No, messages are encrypted end-to-end. Only participants in a conversation have the keys to decrypt the messages in it. Your app cannot decrypt messages either.
2627
+
2628
+
2. **How does XMTP's encryption compare to Signal or WhatsApp?**
2629
+
2630
+
XMTP provides the same security properties (forward secrecy and post-compromise security) as Signal and WhatsApp, using the newer, more efficient MLS protocol.
2631
+
2632
+
3. **Can others see who users are messaging with?**
2633
+
2634
+
No. Message recipients are encrypted, so even network nodes cannot see who is messaging whom. Nodes can only see timing and size of encrypted messages.
2635
+
2636
+
4. **What happens if a user loses access to their wallet?**
2637
+
2638
+
They'll need to start new conversations from their new wallet. Messages sent to their old wallet address can't be decrypted without access to that wallet.
2639
+
2640
+
5. **Are group messages as secure as direct messages?**
2641
+
2642
+
Yes, MLS provides the same security properties for both group and direct messages. In fact, MLS is particularly efficient for group messaging.
2643
+
2644
+
6. **What if a user suspects their wallet is compromised?**
2645
+
2646
+
Due to forward secrecy, even if someone gains access to their wallet, they can't read their past messages. They should start using a new wallet immediately - this ensures attackers won't be able to read future messages either.
2647
+
2648
+
7. **How does encryption work across different XMTP apps?**
2649
+
2650
+
All XMTP apps use the same MLS protocol, ensuring consistent encryption across the ecosystem regardless of which app users choose.
2651
+
2652
+
2653
+
## pages/protocol/identity.mdx
2654
+
# Identity model with XMTP
2655
+
2656
+
XMTP's identity model includes an inbox ID and its associated identities and installations.
2657
+
2658
+
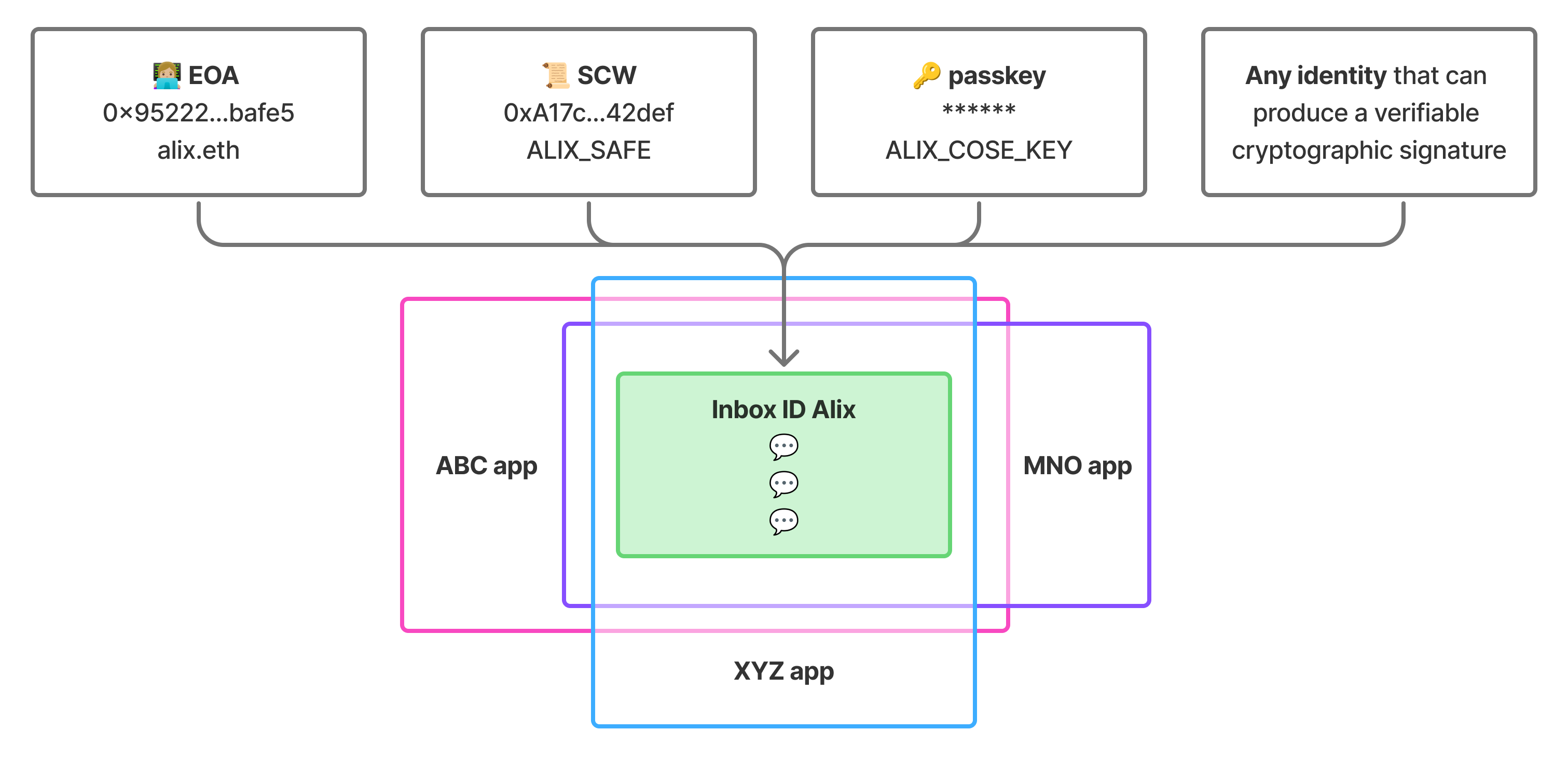
With an inbox ID at its core, instead of a specific wallet address or other identity value, the model is designed for extensibility. A user can associate any number of identity types to their inbox ID and use them to send and receive messages. This gives the user the freedom to add and remove identity types as they naturally change over time, while maintaining the same stable inbox destination for their messages.
2659
+
2660
+
2661
+
2662
+
The identity model also allows XMTP to support any identity type, as long as it can produce a verifiable cryptographic signature. Currently supported identity types include Ethereum EOAs, Ethereum smart contract wallets, and passkeys.
2663
+
2664
+
## Inbox ID
2665
+
2666
+
An **inbox ID** is a user's stable destination for their messages. Their inbox ID remains constant even as they add or remove [identities](#identity) and [installations](#installations).
2667
+
2668
+
The inbox ID is derived from the hash of the first associated wallet address and a nonce and acts as an opaque identifier that apps use for messaging.
2669
+
2670
+
## Identity
2671
+
2672
+
An **identity** is an addressable account that can be associated with an inbox ID. Each identity has a type (like EOA, smart contract wallet, or passkey) and an identifier (like an Ethereum address).
2673
+
2674
+
- Multiple identities can be linked to a single inbox ID
2675
+
- The first identity becomes the **recovery identity** with special privileges
2676
+
- All messages sent to any associated identity are delivered to the same inbox
2677
+
- Any identity that can produce a verifiable cryptographic signature can be supported by XMTP
2678
+
2679
+
## Installation
2680
+
2681
+
An **installation** represents a specific app installation that can access an inbox. Each installation has its own cryptographic keys for signing messages and participating in conversations.
2682
+
2683
+
- Generated automatically when `Client.create()` is called for the first time with an identity that hasn't been used with XMTP before
2684
+
- Multiple installations can access the same inbox (up to 10)
2685
+
- Installations can be revoked by the recovery identity
2686
+
2687
+
## Relationships
2688
+
2689
+
**One inbox ID** → **multiple identities**: Users can receive messages as any of their identities, all flowing to the same inbox
2690
+
2691
+
```
2692
+
Inbox ID (stable destination for messages)
2693
+
├── Identity 1 (recovery identity, first identity added to an inbox)
2694
+
├── Identity 2 (EOA wallet)
2695
+
├── Identity 3 (SCW wallet)
2696
+
└── Any identity that can produce a verifiable cryptographic signature
2697
+
```
2698
+
2699
+
**One identity** → **multiple installations**: Users can access their messages from different apps on the same or different devices
2700
+
2701
+
```
2702
+
Each identity can authenticate new installations:
2703
+
├── Installation A (phone app)
2704
+
├── Installation B (web app)
2705
+
├── Installation C (desktop app)
2706
+
└── Up to 10 installations
2707
+
```
2708
+
2709
+
## Identity actions
2710
+
2711
+
To learn how to build agents with identity actions, see [Manage XMTP inboxes, identities, and installations](/agents/core-messaging/agent-installations).
2712
+
2713
+
To learn how to build chat apps with identity actions, see [Manage XMTP inboxes, identities, and installations](/chat-apps/core-messaging/manage-inboxes).
2714
+
2596
2715
2597
2716
## pages/protocol/epochs.mdx
2598
2717
# Epochs with XMTP
@@ -11217,4 +11336,4 @@ Is your app using a great third-party or public good tool to help with spam and
0 commit comments