forked from vesoft-inc/nebula-docs
-
Notifications
You must be signed in to change notification settings - Fork 0
Commit
This commit does not belong to any branch on this repository, and may belong to a fork outside of the repository.
dashboard database user (vesoft-inc#2275)
* dashboard database user * update
- Loading branch information
1 parent
08ee84f
commit 23ba9ea
Showing
8 changed files
with
101 additions
and
60 deletions.
There are no files selected for viewing
This file contains bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
This file contains bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
35 changes: 35 additions & 0 deletions
35
docs-2.0/nebula-dashboard-ent/4.cluster-operator/10.database-user.md
This file contains bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
| Original file line number | Diff line number | Diff line change |
|---|---|---|
| @@ -0,0 +1,35 @@ | ||
| # Database member | ||
|
|
||
| Users can manage account permissions for databases within the cluster, including managing database members and authorizing graph space permissions. | ||
|
|
||
| !!! note | ||
|
|
||
| For managing account privileges in each cluster on the platform, see [Platform member management](../5.account-management.md). | ||
|
|
||
| ## Entry | ||
|
|
||
| 1. At the top navigation bar of the Dashboard Enterprise Edition page, click **Cluster Management**. | ||
| 2. On the right side of the target cluster, click **Detail**. | ||
| 3. On the left-side navigation bar of the page, click **Database user**. | ||
|
|
||
| ## Managing database members | ||
|
|
||
| 1. Select the **Database user** tab. | ||
| 2. Click **Create database user** and fill in the username, password, and IP whitelist. | ||
|
|
||
| !!! note | ||
|
|
||
| To create database users in batches, click **Add** in the upper left corner to add a new line of configuration items. | ||
|
|
||
| 1. Click **Confirm**. | ||
|
|
||
| ## Authorizing graph space permissions | ||
|
|
||
| 1. Select the **Authorization** tab. | ||
| 2. Click **Grant Role** and select the username, the graph space to be authorized, and the role to be authorized. For details on role permissions, see [Roles and privileges](../../7.data-security/1.authentication/3.role-list.md). | ||
|
|
||
| !!! note | ||
|
|
||
| To authorize in batches, click **Add** in the upper left corner to add a new line of configuration items. | ||
|
|
||
| 1. Click **Confirm**. |
2 changes: 1 addition & 1 deletion
2
docs-2.0/nebula-dashboard-ent/4.cluster-operator/7.data-synchronization.md
This file contains bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
21 changes: 0 additions & 21 deletions
21
docs-2.0/nebula-dashboard-ent/4.cluster-operator/operator/member-management.md
This file was deleted.
Oops, something went wrong.
This file contains bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
| Original file line number | Diff line number | Diff line change |
|---|---|---|
| @@ -1,83 +1,89 @@ | ||
| # Authority management | ||
| # Platform member management | ||
|
|
||
| You can log into NebulaGraph Dashboard Enterprise Edition with different types of accounts. Different accounts have different permissions. This article introduces account types, roles, and permissions. | ||
|
|
||
| !!! note | ||
|
|
||
| You need to configure the related protocols before using LDAP accounts or OAuth2.0 accounts. For details, see [Single sign-on](system-settings/single-sign-on.md). | ||
| For managing account privileges on databases within a cluster, see [Database member](4.cluster-operator/10.database-user.md). | ||
|
|
||
| ## Account types | ||
|
|
||
| Once you log into Dashboard Enterprise Edition using the initialized account name `nebula` and password `nebula`, you can create different types of accounts: LDAP accounts, OAuth2.0 accounts and general accounts. | ||
| Once you log into Dashboard Enterprise Edition using the initialized account name `nebula` and password `nebula`, you can create different types of accounts: general accounts and SSO accounts. | ||
|
|
||
| ### LDAP accounts | ||
| ### General accounts | ||
|
|
||
| Dashboard Enterprise Edition enables you to log into it with your enterprise account by accessing [LDAP (Lightweight Directory Access Protocol)](https://ldap.com/). | ||
| Dashboard Enterprise Edition enables you to create local accounts. | ||
|
|
||
| ### OAuth2.0 accounts | ||
| ### SSO accounts | ||
|
|
||
| !!! caution | ||
| !!! note | ||
|
|
||
| The feature is still in beta. It will continue to be optimized. | ||
| SSO (Single Sign On) supports LDAP, OAuth2.0 and CAS. You need to configure the related protocols before using it. For details, see [Single sign-on](system-settings/single-sign-on.md). | ||
|
|
||
| Dashboard Enterprise Edition enables you to use access_token to authorize the third-party applications to access the protected information based on [OAuth2.0](https://oauth.net/2/). | ||
| - LDAP accounts | ||
|
|
||
| ### General accounts | ||
| Dashboard Enterprise Edition enables you to log into it with your enterprise account by accessing [LDAP (Lightweight Directory Access Protocol)](https://ldap.com/). | ||
|
|
||
| Dashboard Enterprise Edition enables you to create local accounts. | ||
| - OAuth2.0 accounts | ||
|
|
||
| ## Account roles | ||
| !!! caution | ||
|
|
||
| You can set different roles for your accounts. Roles are different in permissions. There are two types of account roles in Dashboard Enterprise Edition: system roles (`admin` and `user`) and cluster roles (`owner` and `operator`). | ||
| The feature is still in beta. It will continue to be optimized. | ||
|
|
||
| The relationship between system roles and cluster roles and their descriptions are as follows. | ||
| Dashboard Enterprise Edition enables you to use access_token to authorize the third-party applications to access the protected information based on [OAuth2.0](https://oauth.net/2/). | ||
|
|
||
| 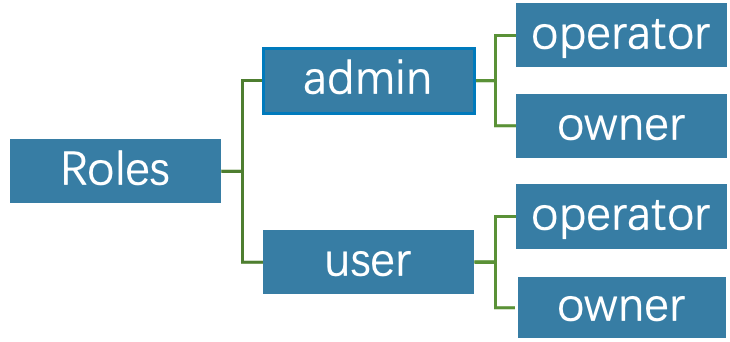 | ||
| - accounts | ||
|
|
||
| **System roles**: | ||
| Dashboard Enterprise Edition enables you to verify your identity based on [CAS (Central Authentication Service)](https://apereo.github.io/cas) 2.0 protocol. | ||
|
|
||
| | Roles | Permission | Description | | ||
| | ------ | ------------------------------------------------------------ | ------------------------------------------------------------ | | ||
| | admin | 1. Create accounts.<br>2. Modify the role of an existing account.<br>3. Perform platform settings, system-level alert settings.<br>4. Delete accounts. | 1. There can be multiple `admin` roles, i.e. system administrators.<br/> 2. An `admin` is the `operator` of all clusters by default, i.e. an `admin` can manage all clusters. <br/>3. An `admin` can assign a `user` to be the `operator` of a cluster.<br/>4. Displayed in the cluster member list by default. An `owner` cannot remove an `admin` unless the `admin` is converted to `user`, and the system will automatically remove the `admin` from the cluster member list. | | ||
| | user | 1. Has read-only permissions for the system dimension. <br/>2. After an `admin` creates a new account with the `user` role, the `user` account cannot view any clusters if the corresponding cluster is not assigned to the account. <br/>3. Can create clusters and become the `owner` of the clusters. | 1. General role. <br/>2. There can be multiple `user` roles. | | ||
| ## Account roles | ||
|
|
||
| You can set different roles for your accounts. Roles have different permissions. There are two types of account roles in Dashboard Enterprise Edition. | ||
|
|
||
| **Cluster roles**: | ||
|  | ||
|
|
||
| | Roles | Permission | Description | | ||
| | ---------- | ------------------------------------------------------------ | ---------------------------------------------------------- | | ||
| | `operator` | 1. Scale clusters. <br/>2. Set cluster alerts. <br/>3. Manage cluster nodes.<br/>4. Manage cluster services. | 1. The cluster operator.<br/> 2. There can be multiple `operator` roles in a cluster. | | ||
| | `owner` | 1. Have all the permissions of `operator`. <br/>2. Unbind and delete clusters.<br/>3. Add and remove accounts with `operator` roles. <br/>4. Transfer the `owner` role. | 1. The cluster owner. <br/>2. There can only be one `owner` in a cluster. | | ||
| - Platform roles: `admin` and `user`. | ||
| - The `admin` role is equivalent to the administrator of the platform, who can manage the platform roles of all accounts, and can perform daily operation and maintenance operations on all clusters. | ||
| - The `user` role is equivalent to a general user of the platform, who can only manage the clusters that the user has created or been authorized to manage. | ||
| - Cluster roles: `owner` and `operator`. | ||
| - The `owner` role represents the owner of a cluster, you can authorize other accounts to manage your clusters. You set yourself up as the `owner` when you create a cluster, and you can transfer the `owner` role to other accounts. | ||
| - The `operator` role means that you can perform daily operations on the cluster, but you cannot transfer the `owner` role, change the cluster database password, unbind the cluster, and delete the cluster. | ||
|
|
||
| ## Create accounts | ||
|
|
||
| Accounts with `admin` roles can create other accounts. The steps are as follows: | ||
|
|
||
| 1. At the top navigation bar of the Dashboard Enterprise Edition page, click **Authority**, and click **Create**. | ||
| 1. At the top navigation bar of the Dashboard Enterprise Edition page, click **Members**, and click **Add**. | ||
| 2. Select one method and input information to create an account, and click **OK**. | ||
|
|
||
| - Invite (LDAP or OAuth2.0 accounts): Set the invitee's account type, enterprise email and role. After the invitee clicks the **Accept** button in the email to activate the account, the invitee needs to click **Login** to automatically jump to the Dashboard Enterprise Edition login page. The invitee can log into Dashboard with his/her enterprise email account and password. | ||
| - Invite (LDAP or OAuth2.0 accounts): Set the invitee's account type, enterprise email, role and authorize cluster. After the invitee clicks the **Accept** button in the email to activate the account, the invitee needs to click **Login** to automatically jump to the Dashboard Enterprise Edition login page. The invitee can log into Dashboard with his/her enterprise email account and password. | ||
|
|
||
| !!! note | ||
|
|
||
| Automatic registration is also supported after LDAP is enabled. When you enter an unregistered account in LDAP mode on the login page, the Dashboard automatically registers the account, but the role permission is `user`. | ||
|
|
||
| - Create Account (general accounts): Set the login name, password, and role for the new account. For information about roles, see the above content. | ||
| - Create Account (general accounts): Set the login name, password, role and authorize cluster for the new account. For information about roles, see the **Account roles** section above. | ||
|
|
||
| ## View accounts | ||
|
|
||
| The created accounts are displayed on the **Authority** page. | ||
|
|
||
| - You can view the username, account type, role, associated cluster, and create time of accounts. | ||
|
|
||
| - **Account Type**: Includes **ldap**, **oauth2.0** and **platform**. **platform** is a general account. | ||
| - **Role**: Displays the role of an account, including **admin** and **user**. For more information about roles, see the above content. | ||
| - **Account Type**: Includes **ldap**, **oauth2.0**, **cas** and **platform**. **platform** is a general account. | ||
| - **Role**: Displays the role of an account, including **admin** and **user**. For more information about roles, see the **Account roles** section above. | ||
| - **Associated Clusters**: Displays all the clusters that can be operated by an account. If the cluster was created by the account, the associated cluster has the `owner` tag. | ||
|
|
||
| - You can search for accounts in the search box, and filter accounts by selecting an associated cluster. | ||
|
|
||
| ## Other operations | ||
|
|
||
| - In the **Action** column on the **Authority** page, click  to edit account information. | ||
| Performing the following operations requires the account to have the associated role permissions. For details on roles, see the **Account Roles** section above. | ||
|
|
||
| - Edit account | ||
|
|
||
| In the **Action** column, click  to edit account information. This includes modifying the account platform role, or authorizing the `operator` role to the account for clusters where you have the `owner` role. | ||
|
|
||
| - Delete account | ||
|
|
||
| - In the **Action** column on the **Authority** page, click  to delete an account. | ||
| In the **Action** column, click  to delete an account. Accounts without the `owner` role can be deleted. |
This file contains bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
This file contains bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters