-
Notifications
You must be signed in to change notification settings - Fork 13
Commit
This commit does not belong to any branch on this repository, and may belong to a fork outside of the repository.
Merge pull request #454 from nextcloud/backport/390/stable25
[stable25] Rename "user" to "account" in description
- Loading branch information
Showing
2 changed files
with
19 additions
and
19 deletions.
There are no files selected for viewing
This file contains bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
| Original file line number | Diff line number | Diff line change |
|---|---|---|
| @@ -1,17 +1,17 @@ | ||
| # BruteForceSettings | ||
|
|
||
| This app provides the possibility to manage some settings of the brute force protection in Nextcloud. | ||
|
|
||
| - [See app in NC AppStore](https://apps.nextcloud.com/apps/bruteforcesettings) | ||
|
|
||
| ## Screenshot | ||
|
|
||
| 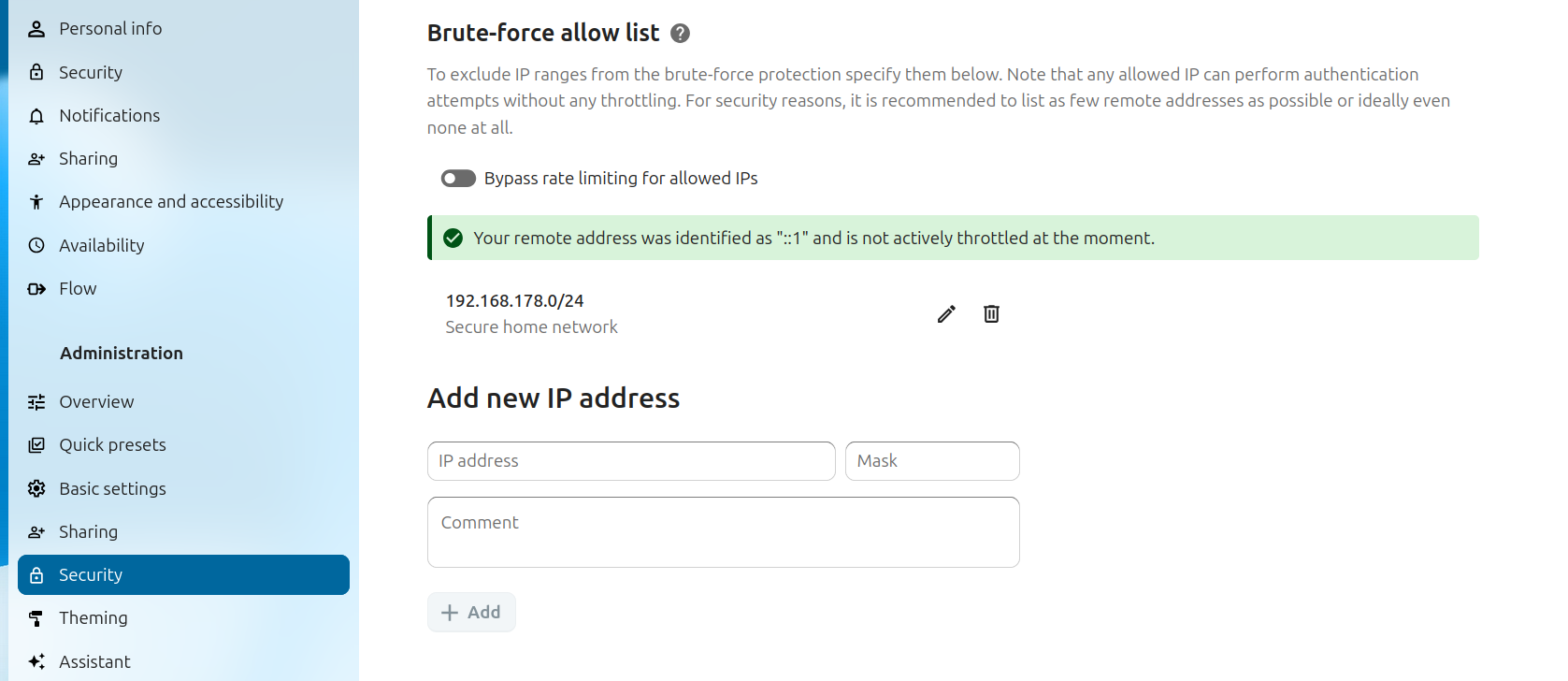 | ||
|
|
||
| ## Description | ||
|
|
||
| Brute Force Protection is meant to protect Nextcloud servers from attempts to guess user passwords in various ways. Besides the obvious "*let's try a big list of commonly used passwords*" attack, it also makes it harder to use slightly more sophisticated attacks via the reset password form or trying to find app password tokens. | ||
|
|
||
| If triggered, brute force protection makes requests coming from an IP on a bruteforce protected controller with the same API slower for a 24 hour period. | ||
|
|
||
| With this app, the admin can exempt an IP address or range from this protection which can be useful for testing purposes or when there are false positives due to a lot of users on one IP address. | ||
| # BruteForceSettings | ||
|
|
||
| This app provides the possibility to manage some settings of the brute force protection in Nextcloud. | ||
|
|
||
| - [See app in NC AppStore](https://apps.nextcloud.com/apps/bruteforcesettings) | ||
|
|
||
| ## Screenshot | ||
|
|
||
| 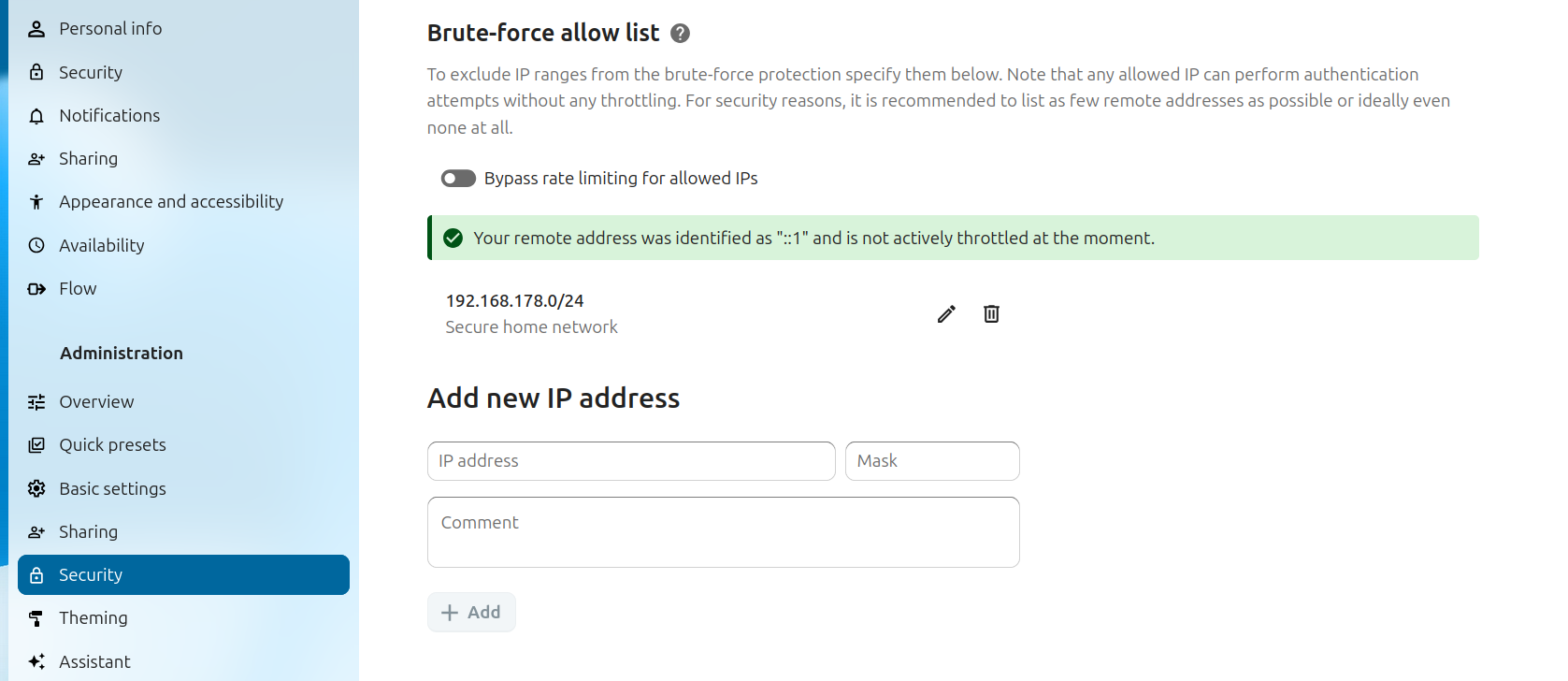 | ||
|
|
||
| ## Description | ||
|
|
||
| Brute Force Protection is meant to protect Nextcloud servers from attempts to guess passwords and tokens in various ways. Besides the obvious "*let's try a big list of commonly used passwords*" attack, it also makes it harder to use slightly more sophisticated attacks via the reset password form or trying to find app password tokens. | ||
|
|
||
| If triggered, brute force protection makes requests coming from an IP on a bruteforce protected controller with the same API slower for a 24 hour period. | ||
|
|
||
| With this app, the admin can exempt an IP address or range from this protection which can be useful for testing purposes or when there are false positives due to a lot of people on a single IP address. |
This file contains bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters