Decentralized Cyber Threat Intelligence Kaizen Framework. https://www.metemcyber.ntt.com
Pricom Mainnet (rpc.metemcyber.ntt.com)
| Contract Name | Address |
|---|---|
| CTICatalog | 0xBcb4b84cdaB65C6e6Efe1697CC41a46D0AEaCA61 |
| CTIBroker | 0xC1814B834E1be7DeE7611fD5F747535369B8683e |
| CTIOperator | 0xd9CfB9276376C613e2f9A1691Ac694293b8c7ce8 |
| metemcyber_util (placeholder) |
0x0e5EECFF51a3ab2221fF6bBd240B20E8933ff28A __$47ceb01e1c551398bb2e8f2c8232f40551$__ |
Metemcyber™ enables security collaboration and assessment all across the organization through the intelligence cycle.
Anyone can make a successful intelligence cycle.
- Content-oriented Workflow
- Comparable Data Analysis Process
- Fault-tolerant Collaboration
- Disclosure Control of CTIs
- Measuring the Cost-Effectiveness of CTIs
- Transparency for Trust
- Monitoring the trading activity of CTIs
- Unlocking achievements based on your contribution.
- MISP-friendly 🤗
This exercise will be performed on the test environment.
apt install build-essential python3-dev
pip install -U pip
pip install -U 'metemcyber[cli]'Check the current configuration:
metemctl config showCreate a new account if no keyfile available:
metemctl account createDisplay your account details you are currently using:
metemctl account show
⚠️ You must agree to the terms of service. This is an experimental project on the enterprise ethereum of NTT Communications. You will get a promo code if you agree to these terms.
Get a promo code via email, and airdrop yourself some ETH to get started:
metemctl account airdrop $PROMOTE_CODE_IN_THE_CONFIRMATION_MAILSearch for the CTI token you want to buy (e.g. OSINT)
metemctl ix search 'OSINT'Enter the index number of the CTI token to be purchased. The CTI token address can also be accepted.
metemctl ix buy $TOKEN_INDEX_OR_ADDRESS
⚠️ If you don't have a global IP address or can't traverse a firewall or NAT, you need an account to use ngrok. Setup a local ngrok environment. Download ngrok and extract it. Open the application directory to put the ngrok executable file there:metemctl open-app-dir$ ls "$(metemctl open-app-dir --print-only)" external-links.json metemctl.ini ngrok ...Ngrok need to connect your ngrok account. Make sure the ngrok authtoken exists after ngrok setup:
cat ~/.ngrok2/ngrok.ymlChange the configurations so that the daemon to receive data uses ngrok (from 0 to 1):
metemctl config edit ... [seeker] ... ngrok = 1
Start a seeker daemon to receive data.
metemctl seeker start
metemctl seeker statusUse the CTI token to receive MISP objects at the configured public IP/URL.
metemctl ix use $TOKEN_INDEX_OR_ADDRESSIf you want to use specific IP/URL, you need to tell the Solver daemon your global IP/URL and port number:
metemctl ix use --seeker http(s)://$ADDR:$PORT $TOKEN_INDEX_OR_ADDRESS
In this section, you will run the intelligence cycle using the exercise ir-exercise for Incident Response.
⚠️ You need to enable the test catalog as primary catalog. Enable the test catalog & Disable the production catalog:metemctl ix catalog enable 0x168DD95472cEaF5c28447C8b07A593e205E92A12 # test metemctl ix catalog disable 0xBcb4b84cdaB65C6e6Efe1697CC41a46D0AEaCA61 # productionCheck your catalog settings:
$ metemctl ix catalog show Catalogs *:active *1 0x168DD95472cEaF5c28447C8b07A593e205E92A12 # test 2 0xBcb4b84cdaB65C6e6Efe1697CC41a46D0AEaCA61 # production
Metemcyber can be used not only for CTI dissemination but also CTI creation.
metemctl new --starter=ir-exerciseImplement the analysis process into your workflow by selecting the event ID (In many cases, the same as the UUID of MISP object), the category of CTI (Fraud, Incident Response, Risk Analysis, Security Operations, Security Leadership, Vulnerability Management), and the content(IOCs, TTPs, etc.) you want to include in the CTI.
This is an important piece of evidence to check the "Direction" step in the intelligence cycle.
Select Intelligence Category (Fraud, IR, RA, SecOps, SecLead, Vuln) [IR]:
Input a new event_id(UUID) [70be8ba5-fa7f-4b8e-aa04-dc76e0fa8c42]:
0: IOC
1: TTP
2: Workflow
Choose contents to be include [0,1]:
================================================================
Event ID: 70be8ba5-fa7f-4b8e-aa04-dc76e0fa8c42
Category: Incident Response
Contents: ['TTPs', 'IOCs']
================================================================
Are you sure you want to create it? [y/N]:
⚠️ Make sure Seeker is running to receive the data.metemctl seeker status
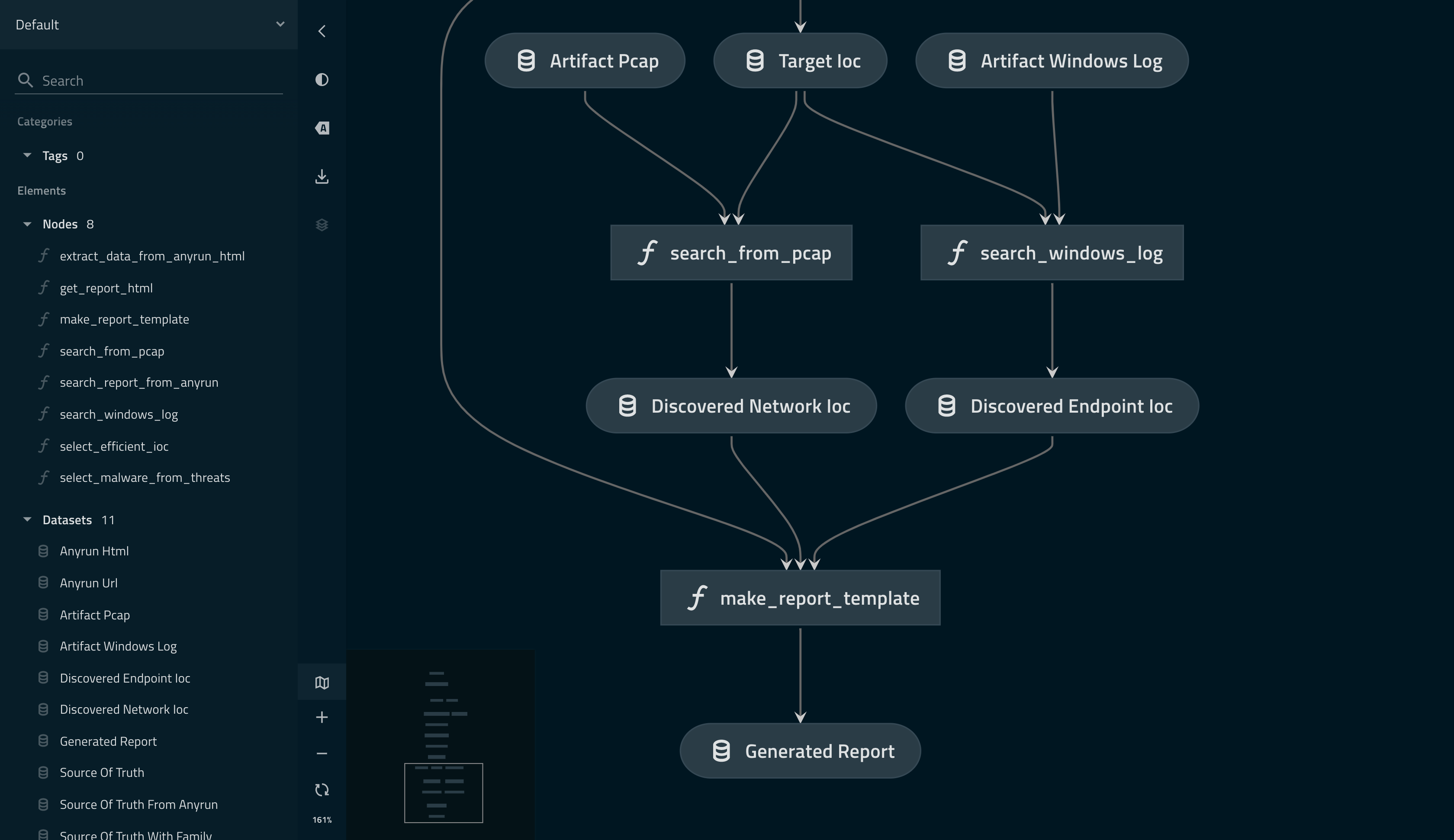
You need to use Kedro to summarize your data analysis process into a workflow.
In practice, it is difficult to clearly separate the steps of "Collection", "Processing" and "Analysis" in the intelligence cycle, which makes the data analysis process look complicated.
Please keep the following two points to make the data analysis process more maintainable.
- Using the Kedro pipeline to describe Analysis Strategy
- Using the Kedro nodes to describe Analysis Method
These are important pieces of evidence to check the "Processing" and "Analysis" step in the intelligence cycle.
For the success of the intelligence cycle, we are more focused on evaluating the data analysis process than on automating the CTI consumption process.
Get data for the exercise ir-exercise:
metemctl ix search '[ir-exercise]'
metemctl ix buy $TOKEN_INDEX_OR_ADDRESS
metemctl ix use $TOKEN_INDEX_OR_ADDRESS
metemctl ix extract $TOKEN_INDEX_OR_ADDRESSRun the ir-exercise workflow:
metemctl run --setupCheck the contents of your CTI product and the workflow:
metemctl check --vizThe --viz option allows you to visualize your data analysis process described by the workflow. (the same as kedro viz)
⚠️ Solver must be running to send the data to token holders.metemctl solver start --enableMISP objects can be distributed when Solver is working properly.
$ metemctl solver status Solver running with operator you configured(0xe889b84a209719B8f0272376dB49946DbD177aE6).
metemctl publish🎉🎉🎉 Welcome to Metemcyber! 🎉🎉🎉
For more information see the documentation.
Copyright 2021 NTT Communications Corporation
Licensed under the Apache License, Version 2.0 (the "License");
you may not use this file except in compliance with the License.
You may obtain a copy of the License at
http://www.apache.org/licenses/LICENSE-2.0
Unless required by applicable law or agreed to in writing, software
distributed under the License is distributed on an "AS IS" BASIS,
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
See the License for the specific language governing permissions and
limitations under the License.