- Architecture
- Concurrency
- Java
- General Questions
- WEB
- SQL
- NoSQL
- Transactions
- Scalability
- Load balancing
- Cloud computing
- Distributed
- Cache
- Networking
- Operating system
- Compilers
- C++
- Javascript
- Python
- Go
- Code writing
- Functional programming
- Reactive programming
- Git
- DevOps
- QA
- Agile, Scrum, XP
- Algorithms
- UML
- Other
- Machine learning
- Big Data
- Image processing
- Cryptography
- Security
- Android
- Books
- Design principles. (DRY, KISS, YAGNI, Occam's razor, Worse is better, convention over configuration, separation of concerns, Law of Demeter (principle of least knowledge), boy scout rule, single source of truth, single version of truth, principle of least astonishment, let it crash principle, inversion of control)
- SOLID
| Rule | Description |
|---|---|
| Single responsibility principle | A module should be responsible to one, and only one, actor. |
| Open/closed principle | A software artifact should be open for extension but closed for modification. |
| Liskov substitution principle | It should be possible to substitute the derived class with base class. |
| Interface segregation principle | Many client-specific interfaces are better than one general-purpose interface. |
| Dependency inversion principle | Depend upon Abstractions but not on concretions. This means that each module should be separated from other using an abstract layer which binds them together. Source code dependency points in the opposite direction compared to the flow of control. |
- The Clean Architecture
- Clean Code Cheat Sheet
- One key abstraction
- Aspect-oriented programming
- The Twelve-Factor App
- Domain-driven design
- Microservices are a style of software architecture that involves delivering systems as a set of very small, granular, independent collaborating services.
- Pros of microservices (The services are easy to replace, Services can be implemented using different programming languages, databases, hardware and software environment, depending on what fits best)
- Design patterns.
- Creational: Builder, Object Pool, Factory Method, Singleton, Multiton, Prototype, Abstract Factory
- Structural: Adapter, Bridge, Composite, Decorator, Facade, Flyweight, Proxy
- Behavioral: Chain of Responsibility, Command, Interpreter, Iterator, Mediator, Memento, Observer, State, Strategy, Template Method, Visitor
- Enterprise integration patterns, SOA patterns.
- 3-tier architecture (Presentation tier, Application tier, Data tier)
- 3-layer architecture (DAO (Repository), Business (Service) layer, Controller)
- REST (Representational state transfer), RPC
- Idempotent operation (The PUT and DELETE methods are referred to as idempotent, meaning that the operation will produce the same result no matter how many times it is repeated)
- Nullipotent operation (GET method is a safe method (or nullipotent), meaning that calling it produces no side-effects)
- Naked objects, Restful objects.
- Why do you need web server (tomcat, jetty)?
- Inheritance vs Composition (Inheritance - is-a relationship, whether clients will want to use the subclass type as a superclass type. Composition - has-a or part-of relationship).
- Multiple inheritance (diamond) problem
- Advantages of using modules. (reuse, decoupling, namespace)
- Drawbacks of not using separation of concerns
- Adding new features will take an order of magnitude longer
- Impossible to optimize
- Extremely difficult to test
- Fixing and debugging can be a nightmare (fixing something in one place can lead to something else breaking that seems completely unrelated).
- What is uniform access principle? (client code should not be affected by a decision to implement an attribute as a field or method)
- Conway's law (organizations which design systems ... are constrained to produce designs which are copies of the communication structures of these organizations)
- GRASP
- What is deadlock, livelock? (Deadlock is a situation in which two or more competing actions are each waiting for the other to finish, and thus neither ever does. A livelock is similar to a deadlock, except that the states of the processes involved in the livelock constantly change with regard to one another, none progressing.)
- Deadlock avoidance. (prevention, detection, avoidance (Mutex hierarchy), and recovery)
- What is starvation? (a problem encountered in concurrent computing where a process is perpetually denied necessary resources to process its work)
- What is race condition? (Behavior of software system where the output is dependent on the sequence or timing of other uncontrollable events)
- What is happens-before relation?
- What is thread contention? (Contention is simply when two threads try to access either the same resource or related resources in such a way that at least one of the contending threads runs more slowly than it would if the other thread(s) were not running). Contention occurs when multiple threads try to acquire a lock at the same time
- What is a thread-safe function? (Can be safely invoked by multiple threads at the same time)
- Publish/Subscribe pattern
- What is 2-phase locking? (Growing phase, shrinking phase. Guarantees serializablity for transactions, doesn't prevent deadlock).
- What is the difference between thread and process? (Threads (of the same process) run in a shared memory space, while processes run in separate memory spaces)
- What is false sharing, cache pollution, cache miss, thread affinity, ABA-problem, speculative execution?
- What is a lock-free, wait-free, obstruction-free algorithm?
- What is sequential consistency? (The result of any execution is the same as if the operations of all the processors were executed in some sequential order, and the operations of each individual processor appear in this sequence in the order specified by its program).
- What is a memory barrier? (A memory barrier, also known as a membar, memory fence or fence instruction, is a type of barrier instruction that causes a CPU or compiler to enforce an ordering constraint on memory operations issued before and after the barrier instruction)
- Synchonization aids in Java
- CountDownLatch
- CyclicBarrier
- Phaser
- ReentrantLock
- Exchanger
- Semaphore
- LinkedTransferQueue
- What is data race? (When a program contains two conflicting accesses that are not ordered by a happens-before relationship, it is said to contain a data race. Two accesses to (reads of or writes to) the same variable are said to be conflicting if at least one of the accesses is a write)
- Java memory model. (A program is correctly synchronized if and only if all sequentially consistent executions are free of data races. Correctly synchronized programs have sequentially consistent semantics. Causality requirement for incorrectly synchronized programs. link)
- What is monitor in Java? (Each object in Java is associated with a monitor, which a thread can lock or unlock)
- What is safe publication?
- What is wait/notify?
- Amdahl's law? (Speedup = 1 / (1 - p + p / n))
- Dining philosophers problem (Resource hierarchy (first take lower-indexed fork), arbitrator, communication (dirty/clean forks)).
- Produces/consumer problem.
- Readers/writers problem.
- Transactional memory
- Coroutine
- PhantomReference, WeakReference, SoftReference, finalize(), ReferenceQueue.
- How to correctly stop a thread? (Thread.interrupt())
- What is Spring? (Spring Framework is an application container for Java that supplies many useful features, such as Inversion of Control, Dependency Injection, abstract data access, transaction management, and more)
- Spring is a framework for dependency injection: a design pattern that allows the developer to build very decoupled systems by injecting dependencies into classes.
- It elegantly wraps Java libraries and makes then much easier to use in your application.
- Included in the framework are implementations of commonly used patterns such as REST and MVC web framework which are predominately use by in web applications.
- What is Spring-Boot?
- What is Hibernate and JPA (Caches, lazy-loading)?
- Garbage collection. (G1, Young/Old generation collectors combination examples: PS Scavenge/PS MarkSweep, Copy/MarkSweepCompact)
- How to write benchmarks? (jmh)
- What are Java 9 modularity?
- What is OSGI? (Specification describes a modular system and a service platform for the Java programming language that implements a complete and dynamic component model. Each bundle has its own classpath. Dependency hell avoidance. META-INF/MANIFEST.MF contains OSGI-info)
- Serializable / Externalizable
- What is a servlet (versions of servlet api, Servlet 4.0)?
- What is a servlet filter? How to implement GZipFilter? (ResponseWrapper)
- What is generics and PECS (producer extends and consumer super)?
- What is the difference between <?>, <Object>, <? extends Object> and no generic type? link1 link2
- Explain method signature for Collections.max(...), Collections.fill(...), Collections.copy(...), Collections.sort(...)
- Why are arrays covariant but generics are invariant? link
- Major specs: JAX-RS, JAX-WS, JMS, JAXB, XSLT, XPATH, JNDI, JMX, JDBC, XML(SAX, DOM, StAX)
- Polymorphism (Variable of type Shape could refer to an object of type Square, Circle... Ability of a function to handle objects of many types)
- Encapsulation (Packing of data and functions into a single component)
- Virtual function (Overridable function)
- Virtual method table
- Dynamic binding (Actual method implementation invoked is determined at run time based on the class of the object, not the type of the variable or expression)
- How does garbage collector work? (Mark and sweep: mark: traverse object graph starting from root objects, sweep: garbage collect unmarked objects. Optimizations: young/old generations, incremental mark and sweep)
- Tail recursion (A tail call is a subroutine call performed as the final action of a procedure)
- Semantic versioning
- WEB security vulnerabilities (XSS, CSRF, session fixation, SQL injection, man-in-the-middle, buffer overflow)
- CSRF prevention (CSRF-token)
- What is JSONP, CORS? (A communication technique used in JavaScript programs running in web browsers to request data from a server in a different domain, something prohibited by typical web browsers because of the same-origin policy)
- HTTPS negotiation steps.
- What is HTTP Strict Transport Security (HSTS)? (Prevents Man in the Middle attacks)
- Browser-server communication methods: WebSocket, EventSource, Comet(Polling, Long-Polling, Streaming)
- Character encoding
- What is role-based access control and access control list?
- What is session and persistent cookies, sessionStorage and localStorage?
- How to implement remember-me? (http://jaspan.com/improved_persistent_login_cookie_best_practice)
- Authentication using cookies, JWT (JSON Web Tokens).
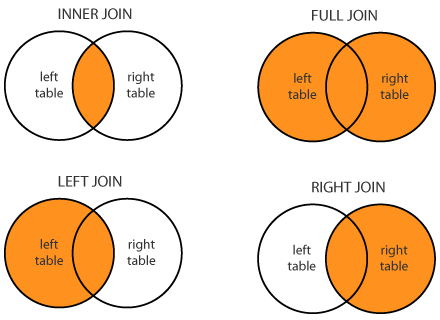
- SQL join types (inner join, left/right outer join, full outer join, cross join)
)
- SQL normal forms
- The domain of each attribute contains only atomic values, and the value of each attribute contains only a single value from that domain
- No non-prime attribute in the table is functionally dependent on a proper subset of any candidate key
- Every non-prime attribute is non-transitively dependent on every candidate key in the table. BCNF.Every non-trivial functional dependency in the table is a dependency on a superkey.)
- Isolation levels and Anomalies
| Isolation_level\Anomaly | Lost_update (because of rollback) | Dirty_read | Non_repeatable_reads second_lost_update | Phantoms | Write_skew |
|---|---|---|---|---|---|
| Read Uncommitted | - | may occur | may occur | may occur | may occur |
| Read Committed | - | - | may occur | may occur | may occur |
| Repeatable Read | - | - | - | may occur | may occur |
| Snapshot | - | - | - | - | may occur |
| Serializable | - | - | - | - | - |
- Types of NoSQL databases?
- Document Stores (MongoDB, Couchbase)
- Key-Value Stores (Redis, Volgemort)
- Column Stores (Cassandra)
- Graph Stores (Neo4j, Giraph)
- ACID
- 2-phase commit protocol
- 3-phase commit protocol
- What is pessimistic / optimistic locking?
- Horizontal and vertical scaling.
- How to scale database? (Data partitioning, sharding(vertical/horizontal), replication(master-slave, master-master)).
- Denormalization.
- What is synchronous multimaster replication? (Each server can accept write requests, and modified data is transmitted from the original server to every other server before each transaction commits)
- What is asynchronous multimaster replication? (Each server works independently, and periodically communicates with the other servers to identify conflicting transactions. The conflicts can be resolved by users or conflict resolution rules)
- When to use messaging queue?
- MongoDB, Redis.
- Hadoop basics.
- sticky/non-sticky sessions
- Sticky sessions vs storing sessions in Redis.
- What is cloud computing? (Cloud computing platform is a fully automated server platform that allows users to purchase, remotely create, dynamically scale, and administer system)
- Amazon web services
- Google Cloud Platform
- Microsoft Azure
- Consensus
- Raft (In Search of an Understandable Consensus Algorithm)
- Paxos
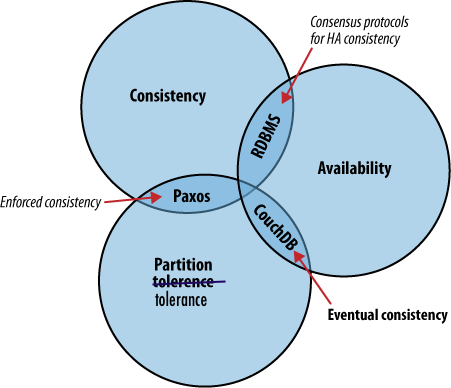
- What is CAP theorem? Illustrated proof (It is impossible for a distributed computer system to simultaneously provide all three of the following guarantees: consistency, availability, partition tolerance). Gilbert and Lynch's paper. "Please stop calling databases CP or AP")
- What is map-reduce? (Word count example)
- Sharding counters.
- Distributed software:
- Distributed streaming platforms: kafka
- Distributed key-value store: zookeeper, etcd, Consul
- Map-reduce: hadoop, spark
- Distributed file system: hbase
- Cluster management: kubernetes, docker-swarm, mesos
- Herlihy’s consensus hierarchy. Every shared object can be assigned a consensus number, which is the maximum number of processes for which the object can solve wait-free consensus in an asynchronous system.
1 Read-write registers
2 Test-and-set, swap, fetch-and-add, queue, stack
⋮ ⋮
∞ Augmented queue, compare-and-swap, sticky byte
- Consistency models:
- Consensus number. Maximum number of threads for which objects of the class can solve consensus problem.
- Logical clock
- Vector clock
- What is write-through and write-behind caching? (write-through (synchronous), write-behind (asynchronous))
- HTTP cache options?
- OSI model (Physical, Data link, Network, Transport, Session, Presentation, Application)
- Multithreading vs select
- Switch, hub, router
- TCP congestion
- TCP back-pressure
- What is memory mapped file and its benefits?
- Interprocess communication methods. (Pipes, Events, Mailboxes/Ports (can be implemented by using shared memory and semaphores), Direct Message Passing).
- Virtual memory organization.
- Process scheduler.
- this keyword
- How prototypes work?
- inheritance
- differences between == and === (http://dorey.github.io/JavaScript-Equality-Table/)
- closures
- recursion
- What is MVC, MVP, MVVM?
- What is promise?
- What is event bubbling and capturing? (target.addEventListener(type, listener[, useCapture]))
- What is AMD(Asynchronous Module Design) and CommonJS?
- What is jQuery?
- Implement binary search
int binarySearch(int[] a, int fromInclusive, int toExclusive, int key) {
int low = fromInclusive;
int high = toExclusive - 1;
while (low <= high) {
int mid = (low + high) >>> 1;
int midVal = a[mid];
if (midVal < key)
low = mid + 1;
else if (midVal > key)
high = mid - 1;
else
return mid; // key found
}
return -(low + 1); // key not found
}- Implement quick sort
void qSort(int[] a, int fromInclusive, int toInclusive) {
int i = fromInclusive;
int j = toInclusive;
if (i >= j) return;
int separator = a[i + random.nextInt(j - i + 1)];
do {
while (a[i] < separator) ++i;
while (a[j] > separator) --j;
if (i > j) break;
int t = a[i];
a[i] = a[j];
a[j] = t;
++i;
--j;
} while (i <= j);
qSort(a, fromInclusive, j);
qSort(a, i, toInclusive);
}- Referential transparency
- What is Monad?
- The Reactive Manifesto (responsive, resilient, elastic, message driven)
- Reactive extensions
- What is asynchronous and non-blocking? link
- Git workflow? (Master: production-ready state; Develop: latest delivered development changes for the next release; Feature Branches; Release Branches; Hotfixes)
http://nvie.com/posts/a-successful-git-branching-model/
- What is a rebase?
- What is Blue-green Deployment, Canary release, A/B testing? link
- What is Docker?
- What is unit test? (A test that purely tests a single unit of functionality)
- What is component test?
- What is integration test? (Examine several parts of a system to make sure that when integrated, these parts behave as expected)
- What is user acceptance test? BDD?
- Unit tests advantages?
- Types of tests: acceptance testing, functional testing, smoke testing, regression testing, unit testing, integration testing, stress testing, (Load, Performance, Sanity, Stability, Security, Feature, Progression, Installation, Business).
- Differences between stub and mock? (A stub is a test double with preprogrammed behavior. Mocks are stubs with preprogrammed expectations)
- Selenium tests and webdriver.
- How to test multithreading code?
- What is Consumer Driven Contract? link
- Types of tests
- What is Agile? (http://agilemanifesto.org/principles.html)
- Individuals and interactions over Processes and tools
- Working software over Comprehensive documentation
- Customer collaboration over Contract negotiation
- Responding to change over Following a plan
- What is Scrum? (Roles: product owner, development team, scrum master. Events: sprint)
- What are the differences between Scrum and Waterfall? ( http://www.leanagiletraining.com/agile/waterfall-versus-scrum-how-do-they-compare/)
- What is XP? ()
- What is Kanban?
- What is Lean development?
- What Ο(n), Ω(n), Θ(n)?
- What is NP, NP-completeness, NP-hardness with examples?
- How to find memory leak. (Memory snapshot diff).
- Profiling: sampling and instrumentation.
- Regular expressions. (Examples)
- What are your goals to work in our company? (3 categories: professional, financial, social)
- What is virtualization?
- What is total/partial order?
- How to work with legacy code? (http://programmers.stackexchange.com/a/122024)
- Confidence interval
- p-value
- Overfitting
- Bias–variance tradeoff
- Backpropagation
- Reinforcement learning
- Curse of dimensionality
- Cross-validation
- Bag-of-words, Stop words, n-gram, tf–idf, Latent semantic analysis
- Linear regression
- Logistic regression
- Naive Bayes classifier
- Support vector machine
- Principal component analysis
- Deep learning
select 2 primes: p,q
n = p*q
phi(n) = (p-1)*(q-1)
select 1<e<phi(n), gcd(e,phi(n))=1
d=e^-1 mod phi(n)
(e,n) - public key
(d,n) - private key
c = m^e mod n
m = c^d mod n = m^(e*d) mod n = m^(e*d mod phi(n)) mod n = m
- What is OpenID and OAuth2.0 and OpenID Connect?
- Four main actors in an OAuth system (clients, resource owners, authorization servers, and protected resources)
- What is access_token, refresh_token, SAML token, JWT token?
- Sticky session vs Session Replication.
- What is hash salt?
- What is Federated Authentication ?
- What is CSP and SRI hash ?
- What is Clickjacking and Cursorjacking ? How to prevent it ?
- The C++ Programming Language, 4th Edition
- Effective Java (3rd Edition)
- Introduction to Algorithms, 3rd Edition
- The Art of Computer Programming
- Network Flows: Theory, Algorithms, and Applications
- Computational Geometry: Algorithms and Applications
- Algorithms on Strings, Trees, and Sequences
- Compilers: Principles, Techniques, and Tools
- How to Solve It: Modern Heuristics
- Java Concurrency in Practice
- The Art of Multiprocessor Programming
- Reactive Programming with RxJava
- Design Patterns: Elements of Reusable Object-Oriented Software
- Big Data: Principles and best practices of scalable realtime data systems
- Designing Data-Intensive Applications
- Learning From Data
- Kafka: The Definitive Guide
- Cassandra: The Definitive Guide
- The Linux Programming Interface
- Hibernate in Action
- The Garbage Collection Handbook
- Pro Git
- Learning JavaScript
- Clean Code: A Handbook of Agile Software Craftsmanship
- Release It!: Design and Deploy Production-Ready Software