-
Notifications
You must be signed in to change notification settings - Fork 2
CAS postinstall steps
- Table of Contents
- Intro
- CAS keys
- Restart of services after first run
- First user creation
- Authorize IPs to access to user details
- Postfix re-configuration
- Configure cas-management
- Next steps
- End
This page tries to give some additional steps to do after CAS first ansible deployment.
You will need to setup some authentication keys in CAS for a basic usage. La-toolkit will take care of this for you automatically. Else you can either create them manually or copy the autogenerated keys after first start:
These are the ansible variable names for these keys:
pac4j_cookie_signing_keypac4j_cookie_encryption_keycas_webflow_signing_keycas_webflow_encryption_key
You cannot put here and arbitrary string key, because needs to be of some size, etcetera.
More details in: https://apereo.github.io/cas/5.0.x/installation/Configuring-SSO-Session-Cookie.html
Use this script to generate these CAS keys and add them to your ansible inventories, under [cas-servers:vars] group section and re-run ansible to setup them in your server.
Other version of this tool that requires a modern java.
If you run CAS for the first time it will auto-generate these keys for you. Later you can copy-paste in your ansible CAS inventory (see /var/log/atlas/cas/cas.log after first start to copy these autogenerated keys in the inventory).
Sample logs:
2019-08-21 08:14:05,335 INFO [au.org.ala.cas.webflow.AlaCasWebflowConfigurer] - <doInitialize()>
2019-08-21 08:14:08,833 WARN [org.apereo.cas.services.ServiceRegistryInitializer] - <Service registry [MongoDbServiceRegistry] will be auto-initialized from JSON service definitions. This behavior is only useful for testing purposes and MAY NOT be appropriate for production. Consider turning off this behavior via the setting [cas.serviceRegistry.initFromJson=false] and explicitly register definitions in the services registry.>
2019-08-21 08:14:09,239 WARN [org.apereo.cas.services.ServiceRegistryInitializer] - <Skipping [Atlas of Living Australia] JSON service definition as a matching service [Atlas of Living Australia] is found in the registry>
2019-08-21 08:14:09,290 WARN [org.apereo.cas.services.ServiceRegistryInitializer] - <Service registry [MongoDbServiceRegistry] will be auto-initialized from JSON service definitions. This behavior is only useful for testing purposes and MAY NOT be appropriate for production. Consider turning off this behavior via the setting [cas.serviceRegistry.initFromJson=false] and explicitly register definitions in the services registry.>
2019-08-21 08:14:09,293 WARN [org.apereo.cas.services.ServiceRegistryInitializer] - <Skipping [Atlas of Living Australia] JSON service definition as a matching service [Atlas of Living Australia] is found in the registry>
2019-08-21 08:14:10,769 WARN [org.apereo.cas.web.config.CasCookieConfiguration] - <Ticket-granting cookie encryption/signing is turned off. This MAY NOT be safe in a production environment. Consider using other choices to handle encryption, signing and verification of ticket-granting cookies.>
2019-08-21 08:14:11,211 WARN [org.apereo.cas.util.cipher.BaseBinaryCipherExecutor] - <Secret key for signing is not defined under [cas.webflow.crypto.signing.key]. CAS will attempt to auto-generate the signing key>
2019-08-21 08:14:11,214 WARN [org.apereo.cas.util.cipher.BaseBinaryCipherExecutor] - <Generated signing key [tAFV2aeadal_JGhfgPDp4e3UZ0N79qdBND7VSdtU8DoeH_e09rqRtgJvVsHbo7dIvLESnrnkB4mrxtxj73wCcQ] of size [512]. The generated key MUST be added to CAS settings under setting [cas.webflow.crypto.signing.key].>
2019-08-21 08:14:11,214 WARN [org.apereo.cas.util.cipher.BaseBinaryCipherExecutor] - <Secret key for encryption is not defined under [cas.webflow.crypto.encryption.key]. CAS will attempt to auto-generate the encryption key>
2019-08-21 08:14:11,215 WARN [org.apereo.cas.util.cipher.BaseBinaryCipherExecutor] - <Generated encryption key [cVwdaeaDws_QzcIydP5cRg] of size [16]. The generated key MUST be added to CAS settings under setting [cas.webflow.crypto.encryption.key].>If you want to use external authentication providers (like Google, Github, Facebook), you will need keys from the providers you want to use. Some examples are in the local-extras inventory template. See also the OAuth-Authentication Documentation.
Create an oauth application like this in:
https://github.com/settings/applications/new

Configure your inventories with that key/secret:
pac4j_github_consumer_key=XXXXX
pac4j_github_consumer_secret=YYYY
The Google OAUTH is quite similar.
Once CAS is running you will also need to enable those providers in cas-management, see below.
The cas service, at first run, will create its emmet mysql database. userdetails also depends on that database and will not start correctly til cas don't start correctly and create that emmet database.
org.springframework.jdbc.BadSqlGrammarException: Hibernate operation: could not extract ResultSet; bad SQL grammar [n/a]; nested exception is com.mysql.jdbc.exceptions.jdbc4.MySQLSyntaxErrorException: Table 'emmet.role' doesn't existBecause of this, check the status and logs of the different services:
service cas status
service userdetails status
service apikey status
service cas-management statusMany times, after the first deployment and with cas service correctly running (with the generated keys configured), you need to restart the three last services, and then, userdetails can use the emmet recently created database:
service userdetails restart
service apikey restart
service cas-management restartCheck again their status to verify that are running correctly.
If something fails, check the logs for hints.
Now you can register your first user, and give it admin permissions and additional recommended admin roles, following these additional steps.
You have to authorize your IPs in the admin section of userdetails, accessing to something like https://auth.l-a.site/userdetails/admin/authorisedSystem/list. There should be a list of IP address that can access the web services providing user information. Requests from IP addresses not listed there will get a HTTP 403 Forbidden response.
The CAS role install postfix but you should do some extra configuration to setup properly.
You would the default service configured in:
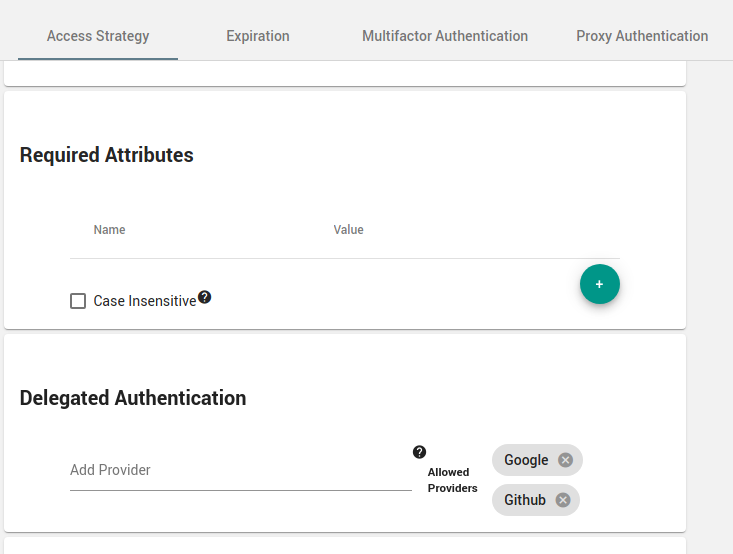
http://auth.l-a.site/cas-management/services/default
changing the name, and adding "Delegated Authentication" if you decide to use Google, Github, Facebook, etc authentication services.
With CAS, userdetails and apikeys running you should create and configure your API Keys in your inventories.
Index
- Wiki home
- Community
- Getting Started
- Support
- Portals in production
- ALA modules
- Demonstration portal
- Data management in ALA Architecture
- DataHub
- Customization
- Internationalization (i18n)
- Administration system
- Contribution to main project
- Study case